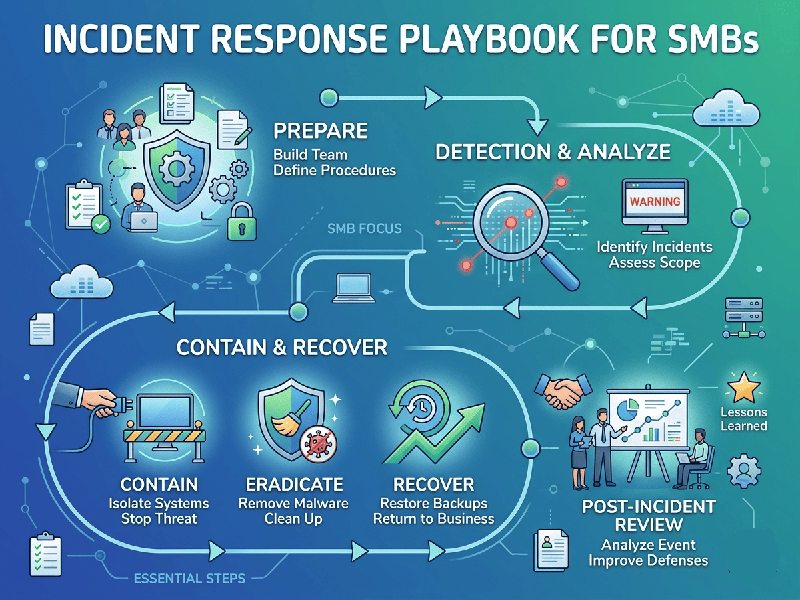
Incident Response Playbook for SMBs
For an SMB, an Incident Response (IR) plan should be actionable,
lightweight, and repeatable. Its goal is to minimize downtime, protect
sensitive data, and maintain customer trust.
Phase 1: Preparation (The Foundation)
- Identify Critical Assets: List your essential hardware,
software, and data repositories (e.g., customer databases, ERP systems).
- Establish a Team: Define who handles what. For an
SMB, this is often the business owner, an IT lead, and an external
consultant or MSP (Managed Service Provider).
- Communication Tree: Have a physical or offline
document containing emergency contact info for all staff, legal counsel,
and the cyber insurance provider.
- Backup Strategy: Ensure immutable, off-site
backups exist. Regularly test your ability to restore from them.
Phase 2: Detection and Analysis
When an anomaly occurs (e.g., suspicious file encryption,
unauthorized logins):
- Verify the Incident: Determine if it is a false
alarm or a genuine breach.
- Scope the Impact: Identify which systems and
accounts are affected.
- Documentation: Start a log immediately. Record
what you saw, when you saw it, and the actions taken. This is critical for
insurance claims and legal requirements.
Phase 3: Containment, Eradication, and Recovery
- Containment: Isolate affected systems.
Unplug network cables or disable compromised network ports to prevent the
spread (e.g., stopping ransomware from encrypting the entire server).
- Eradication: Once contained, identify the
root cause (e.g., a phished password). Delete malware, reset compromised
credentials, and patch the vulnerability.
- Recovery: Restore from clean backups.
Monitor the environment closely for signs of re-infection before going
fully "live" again.
Phase 4: Post-Incident Activity
- Lessons Learned: Hold a meeting with your team
within 48 hours of recovery.
o What went well?
o Where were the delays?
o What tools or training do we need to
prevent this next time?