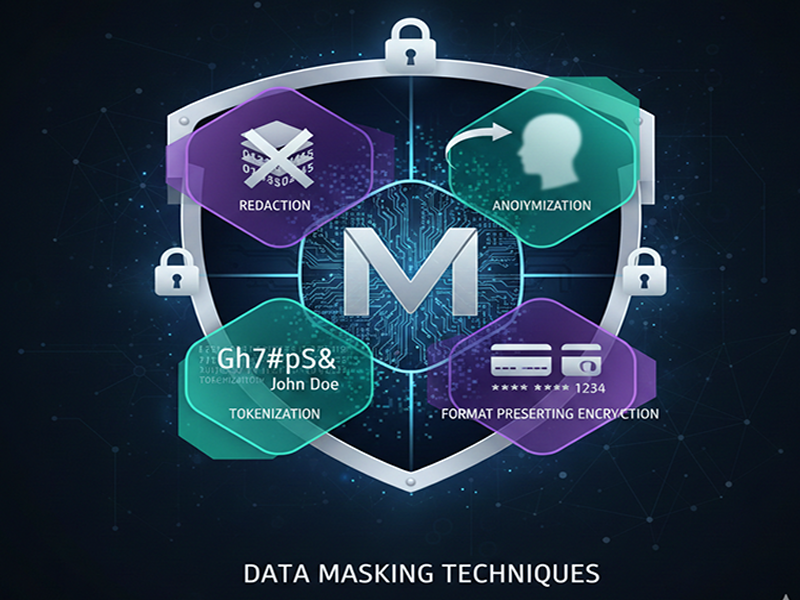
Data Masking Techniques
Data masking
is a critical security process used to create a structurally similar but
inauthentic version of an organization's data. In 2026, it is a "survival
strategy" for businesses to maintain the utility of their data for
development, testing, and AI training while ensuring compliance with global
regulations like GDPR, CCPA, and the EU AI Act.
Core Data
Masking Techniques
- Substitution: Replaces sensitive values
with realistic but fictitious equivalents from a predefined lookup file
(e.g., swapping a real name with one from a diverse list).
- Shuffling: Randomly rearranges values
within a single column, preserving statistical properties while breaking
the link between individual records and their original identities.
- Scrambling: Obfuscates data by
reordering alphanumeric characters (e.g., changing ID "12345" to
"54321"). It is simple but less secure than other methods.
- Masking Out (Redaction): Hides specific parts of a
data string with generic characters like "X" or "*"
(e.g., showing only the last four digits of a credit card).
- Nulling Out (Deletion): Replaces a data field with
a null value or blank space. This is the simplest method but can break
application logic or data integrity.
- Number & Date Variance: Applies a random
percentage (e.g., +/- 10%) or time shift (e.g., +/- 90 days) to numeric
and date fields to keep the dataset statistically useful while preventing
individual identification.
- Pseudonymization: Replaces identifiable data
with aliases. Unlike most masking, this can be reversible if the original
identifiers are stored securely elsewhere.
- Deterministic Masking: Consistently replaces the
same input with the same output across all tables and databases, which is
vital for maintaining referential integrity in complex systems.
Emerging
Trends for 2026
- Synthetic Data Generation: Instead of masking real
records, AI generates entirely artificial datasets that mimic real-world
patterns. By 2026, it is predicted that 75% of businesses will use
generative AI for this purpose.
- AI-Powered Discovery: Modern tools now use Large
Language Models (LLMs) to automatically locate and classify PII
(Personally Identifiable Information) across massive, unstructured data
landscapes.
- Privacy-Enhancing Technologies
(PETs): Advanced
methods like differential privacy (adding mathematical noise) and
homomorphic encryption (enabling analysis on encrypted data) are
increasingly standard