Zero-Trust Access Controls
Understanding Zero-Trust Access Controls (ZTAC)
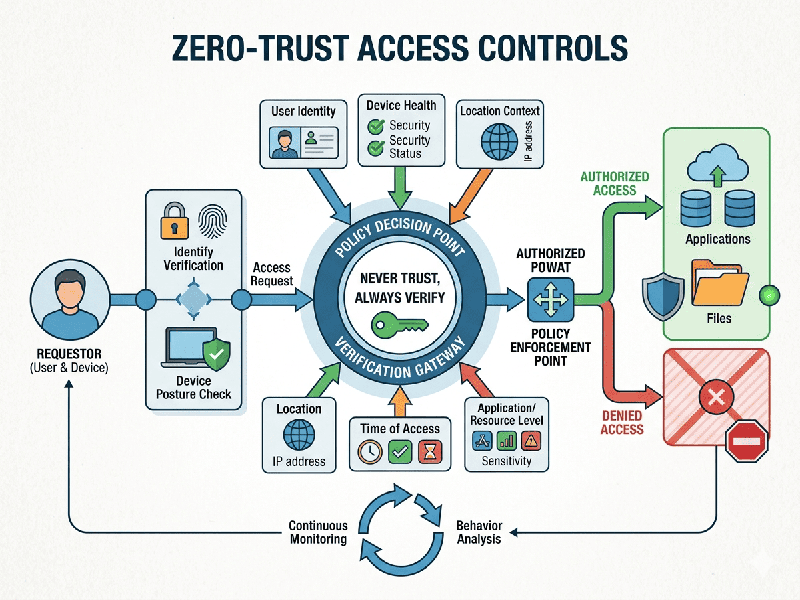
Zero-Trust Access Control (ZTAC) is a security framework
based on the principle of "never trust, always verify." Unlike
traditional security models that assume everything inside a corporate network
is safe, Zero-Trust assumes that threats could exist both outside and inside
the network at all times.
Key Pillars of Zero-Trust
- Identity Verification: Strictly verifying the identity
of every user and device trying to access resources, regardless of their
location.
- Least Privilege Access: Providing users only the
minimum level of access they need to perform their specific tasks,
reducing the "blast radius" if an account is compromised.
- Micro-segmentation: Breaking networks into small,
isolated zones to prevent lateral movement by attackers.
- Continuous Monitoring: Real-time inspection of behavior and environmental context (like time of day or geo-location) to identify anomalies.
The Technical & Architectural View
From an IT infrastructure standpoint, ZTAC is a shift from IP-based
security to Identity-based security. Instead of relying on a
"castle-and-moat" (VPN) strategy, you use a Policy Enforcement
Point (PEP). Every request is intercepted; the system checks the user's
credentials, the device's security posture (is it encrypted?), and the
sensitivity of the data before granting a temporary, encrypted encrypted
"tunnel" to that specific application.