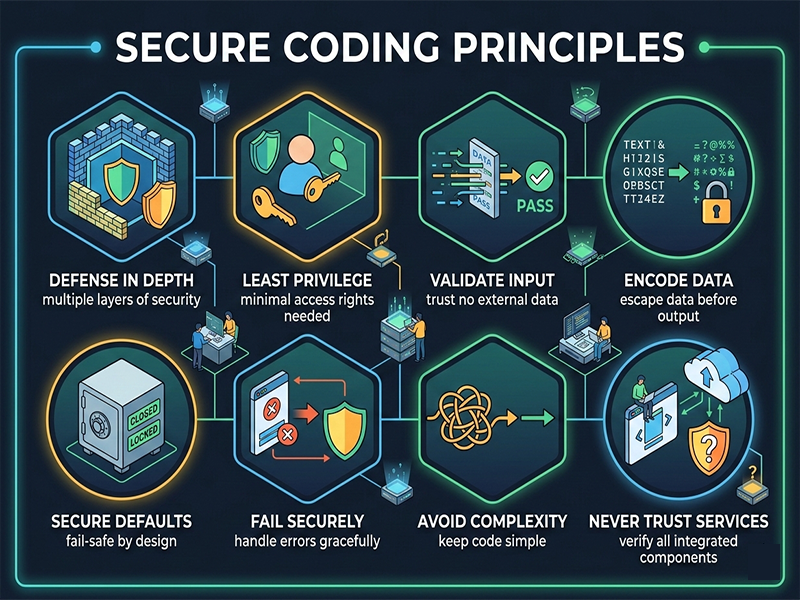
Secure Coding Principles
Secure
coding is no longer an "afterthought" or a final step before
deployment. It is integrated into the developer's daily workflow—often referred
to as Shift-Left Security. The goal is to build software that is
inherently resilient to attacks rather than relying solely on external
firewalls.
1. Least
Privilege
The Principle
of Least Privilege (PoLP) dictates that a code module, process, or user
should only have the minimum level of access necessary to perform its function.
- Application: If an app only needs to read a
database, do not give it "Write" or "Admin"
permissions.
- Benefit: If a specific component is
compromised, the attacker’s "blast radius" is limited to only
what that component could access.
2.
Defense in Depth
Never rely
on a single security measure. Assume that your primary defense will fail and
have redundant layers in place.
- Example: Don't just rely on a firewall.
Use input validation, encrypted storage, and multi-factor authentication
(MFA) simultaneously.
- The "Swiss Cheese"
Model: Even if
one layer has a hole (vulnerability), the other layers catch the threat.
3. Never
Trust User Input (Input Validation)
The #1 cause
of web vulnerabilities (like SQL Injection and XSS) is treating user-provided
data as "safe" code.
- Allow-listing: Only accept what you know is
good (e.g., a zip code should only contain numbers).
- Sanitization: Strip out dangerous characters
like <, >, or ' before processing data.
- Parameterized Queries: Use prepared statements for
database interactions to prevent attackers from "injecting"
their own commands.
4. Fail
Securely
When a
program encounters an error, its default behavior should be to shut down or
restrict access, not to "open the gates."
- Bad Practice: An error occurs in the login
logic, and the system bypasses the password check to keep the app running.
- Good Practice: If an exception occurs during
authentication, the system should default to Access Denied.
- Error Messaging: Never show stack traces or
detailed system info to the end-user. Provide a generic "An error
occurred" message to prevent Information Leakage.
5.
Economy of Mechanism (Keep it Simple)
Complexity
is the enemy of security. The more complex a system is, the harder it is to
audit and the more likely it is to contain "hidden" logic flaws.
- Action: Keep code modular and remove
any "dead code" or unused libraries. In 2026, many attacks
target vulnerabilities in obscure, forgotten dependencies (Software Supply
Chain attacks).
6. Secure
Defaults
A system
should be secure "out of the box." Users should have to manually
opt-in to less secure features, rather than having to opt-out of dangerous
ones.