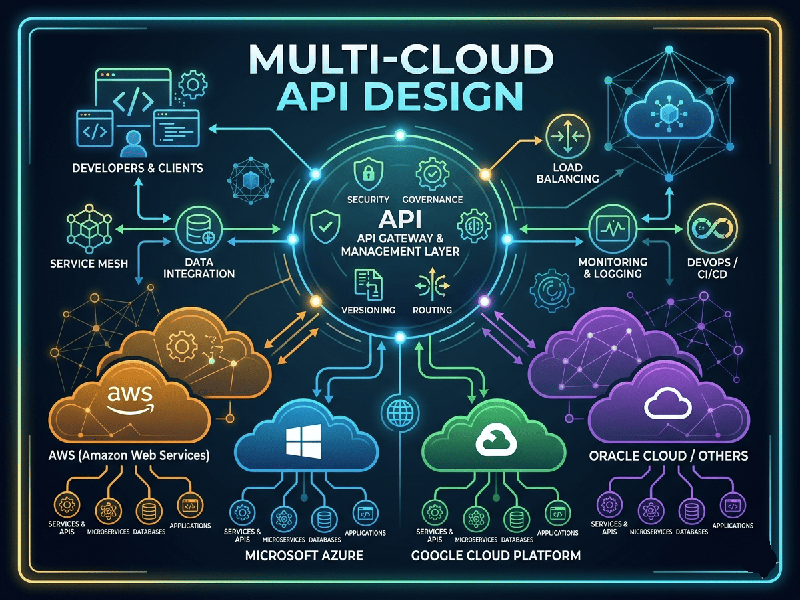
Multi-Cloud API Design
Designing APIs for a multi-cloud environment is like being a
universal translator. You aren’t just building for one ecosystem (like AWS);
you’re building a bridge that stays stable even when the underlying ground (the
cloud provider) shifts.
The goal is cloud-agnosticism: ensuring your services
can move between Azure, GCP, or AWS without rewriting your entire codebase.
1. The Strategy: Abstracting the Infrastructure
The biggest mistake in multi-cloud design is
"leaking" provider-specific logic into your API. If your API expects
an S3 bucket ARN, it will break the moment you move to Google Cloud Storage.
- The Facade Pattern: Use an abstraction layer. Your
API should call a generic uploadFile() method, which then interacts with a
"provider driver" that handles the specifics of S3, Cloud
Storage, or Azure Blobs.
- Standardized Data Formats: Stick to JSON or Protocol
Buffers (gRPC). Avoid vendor-specific binary formats that might be
optimized for one cloud's internal network but sluggish on another.
2. Global Traffic Management
When your API lives in multiple clouds, you need a way to
route users to the right one based on health, latency, or cost.
- Anycast IP / Global Load
Balancing: Use
a global DNS or load balancing service (like Cloudflare or Akamai) that
sits above the cloud providers.
- Service Discovery: Implement a cross-cloud service
mesh (like HashiCorp Consul or Istio) so services in AWS can
find and talk to services in Azure securely.
3. Security and Identity
Each cloud has its own IAM (Identity and Access Management).
Managing these separately is a nightmare.
- OAuth2 and OpenID Connect
(OIDC): Use
these industry standards for authentication.
- Federated Identity: Use a centralized identity
provider (like Okta, Auth0, or Ping) so your API validates tokens against
one source of truth, regardless of where the request lands.
- Mutual TLS (mTLS): Since traffic might travel over
the public internet between clouds, encrypting the communication between
services is non-negotiable.