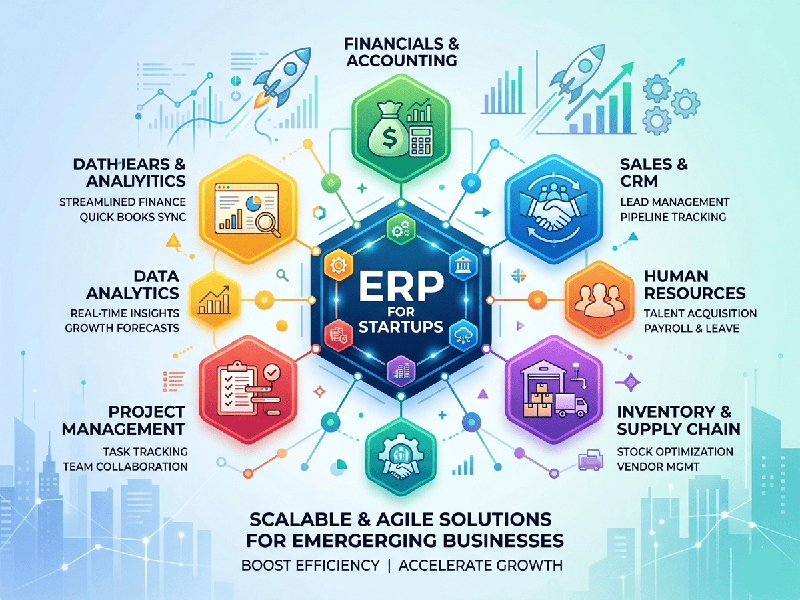
ERP for Startups
Endpoint security is the practice of safeguarding the entry
points (endpoints) of a network—such as laptops, smartphones, and servers—from
being exploited by malicious actors. In 2026, as AI-driven threats and remote
work become the norm, the "essentials" have evolved from simple
antivirus to a multi-layered defense-in-depth strategy.
1. The Core Modern Components
The terminology can be an "alphabet soup," but
these three technologies form the foundation of modern endpoint defense:
- EPP (Endpoint Protection
Platform): The
first line of defense. It focuses on prevention by blocking known
threats (malware, viruses) and using Next-Gen Antivirus (NGAV) to spot
suspicious file behaviors.
- EDR (Endpoint Detection and
Response): The
"security camera" for your device. It continuously monitors and
logs activity to catch the 1% of sophisticated threats that bypass the
EPP. It allows security teams to "roll back" an infected device
to a healthy state.
- XDR (Extended Detection and
Response): The
evolution of EDR. It breaks down silos by correlating data across
endpoints, networks, cloud environments, and email to provide a unified
"big picture" of an attack.
2. The "Zero Trust" Essentials
In 2026, the industry has moved toward a Zero Trust
model: "Never trust, always verify."
- Identity-First Security: Using Multi-Factor
Authentication (MFA) and biometrics as a mandatory requirement for every
device attempting to access the network.
- Least Privilege Access: Ensuring that users and devices
only have the minimum level of access required for their specific job. If
a device is compromised, the attacker is "boxed in" and cannot
move laterally through the network.
- Continuous Posture Checks: Before a device is allowed to
connect, the system checks: Is the OS patched? Is the firewall on? Is it
in a known location? If not, access is denied.
3. Critical Defensive Practices
Beyond software, these operational habits are what prevent
90% of successful breaches:
- Automated Patch Management: Vulnerabilities are weaponized
faster than ever. Automation ensures that critical security updates are
applied to all devices—even those in remote or hybrid settings—within
hours, not weeks.
- Full Disk Encryption (FDE): Essential for mobile
workforces. If a laptop is physically stolen, encryption ensures the data
is unreadable without the key.
- AI-Driven Behavioral Analysis: Modern security tools no longer
just look for "bad files"; they look for "bad
behavior" (e.g., an Excel sheet suddenly trying to run a PowerShell
script), which is a hallmark of fileless malware.