DDoS Mitigation Techniques
IDDoS (Distributed Denial of Service) mitigation has shifted
from simple "traffic blocking" to autonomous, AI-driven defense.
As attackers now use AI to mimic human behavior and launch multi-vector
"hit-and-run" attacks, static rules are no longer enough.
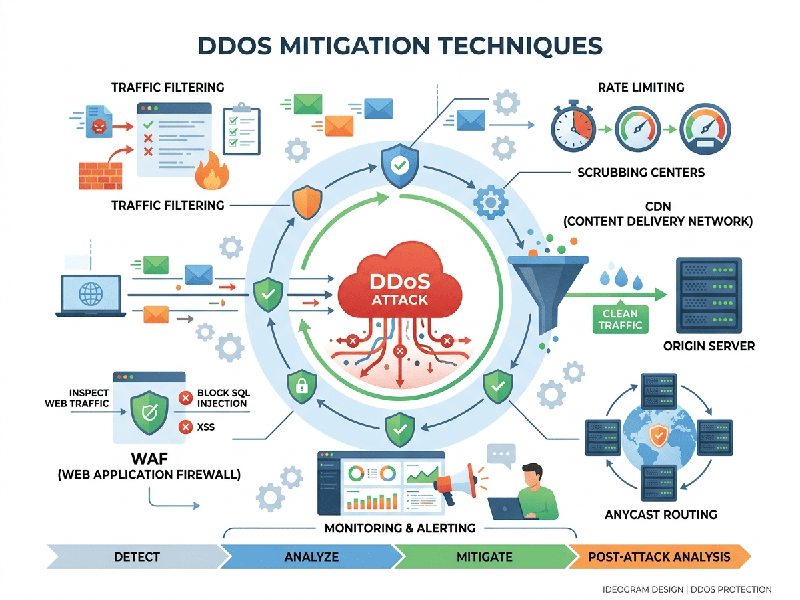
1. Architectural & Infrastructure Defense
These methods reduce your "blast radius" by making
the network more resilient to volume.
- Anycast Network Diffusion: Spreads incoming traffic across
a distributed network of global servers. Instead of one server taking the
full hit, the load is "diluted" across dozens of nodes.
- Attack Surface Reduction: Closing unused ports and
protocols (e.g., blocking UDP if you only use TCP) and hiding origin IP
addresses behind a proxy or Content Delivery Network (CDN).
- Over-provisioning (Bandwidth
Scaling):
Simply "widening the highway" by having more bandwidth than you
realistically need, allowing you to absorb sudden volumetric spikes
without immediate failure.
2. Traffic Filtering & Redirection
These techniques separate the "wheat from the
chaff" during an active attack.
- Scrubbing Centers: Malicious traffic is rerouted
to a high-capacity "scrubbing" facility. There, traffic is
analyzed, the "dirty" attack packets are dropped, and
"clean" legitimate traffic is sent back to the origin.
- Rate Limiting: Restricting the number of
requests a single IP or user can make within a specific timeframe. This is
highly effective against "low and slow" application-layer
attacks.
- Blackhole Routing (Null
Routing): A
"nuclear option" where all traffic to a targeted IP is dropped.
While it stops the attack from crashing the server, it also blocks
legitimate users—essentially completing the attacker's goal for them.
- Sinkholing: Diverting malicious traffic to
a non-existent IP or a "dead end" where it can be analyzed
without affecting the production environment.
3. Advanced AI & Behavioral Mitigation (The 2026
Standard)
Modern attacks often look like legitimate traffic. These
techniques use Machine Learning to spot the difference.
- Behavioral Analysis: Instead of looking for
"known bad" signatures, AI models establish a
"baseline" of normal user behavior. If a group of users starts
clicking buttons or requesting pages in a way that is $0.01\%$
"off," the system flags them.
- Dynamic Fingerprinting: AI identifies specific
"fingerprints" of botnets (like specific browser headers or TLS
handshakes) in real-time and blocks them even as the botnet changes its IP
address.
- Challenge-Response (Captchas
& Beyond):
Modern systems use "invisible challenges" (like browser-based
JavaScript computations) to prove a user is human without interrupting
their experience.