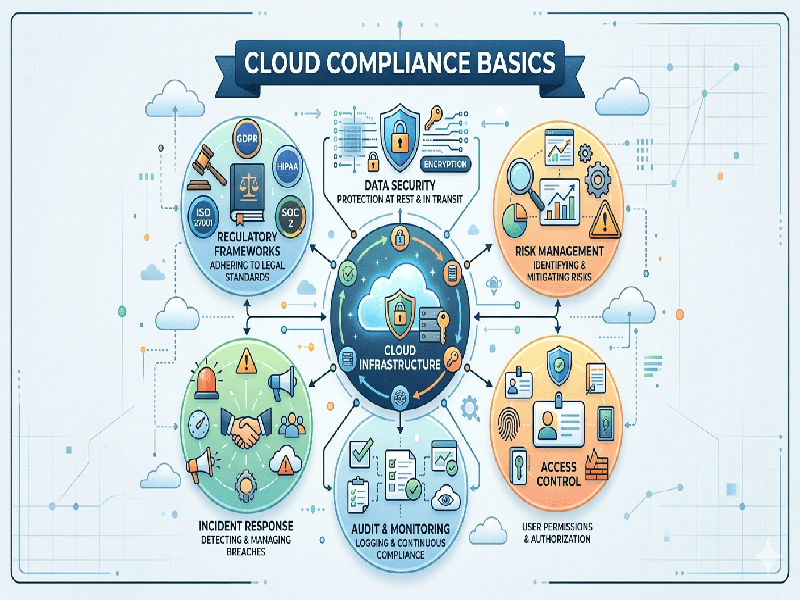
Cloud Compliance Basics
Cloud
compliance is the art and science of ensuring your cloud infrastructure and the
data stored within it meet specific regulatory, legal, and internal security
requirements. It is a shared journey between you and your cloud service
provider (CSP).
1. The
Shared Responsibility Model
The most
critical concept in cloud compliance is knowing where the provider's job ends
and yours begins.
- Compliance OF the Cloud: The CSP (e.g., AWS, Azure,
Google Cloud) is responsible for the physical security of data centers,
hardware, and the virtualization layer.
- Compliance IN the Cloud: You are responsible for
configuring the operating systems, managing user access (IAM), encrypting
data, and ensuring your applications meet specific industry standards.
2. Key
Regulatory Frameworks
Depending on
your industry and geography, you may need to adhere to different standards:
- GDPR (General Data Protection
Regulation):
Mandatory for any business handling the personal data of EU citizens,
focusing on privacy and data sovereignty.
- SOC 2 (System and Organization
Controls): A
technical audit requiring companies to establish and follow strict
information security policies and procedures.
- PCI DSS: Required for any organization
that accepts, transmits, or stores cardholder data.
- ISO/IEC 27001: An international standard for
managing information security systems.
- HIPAA: Specific to the healthcare
industry in the US, ensuring the protection of sensitive patient data.
3. Core
Pillars of a Compliant Cloud
To maintain
a "compliant" status, your architecture should focus on these four
areas:
- Data Residency &
Sovereignty:
Ensuring data is stored in specific geographic regions to satisfy local
laws.
- Identity and Access Management
(IAM):
Implementing "Least Privilege" access—users only have the
permissions they absolutely need.
- Data Encryption: Protecting data both at rest
(stored on disk) and in transit (moving across the internet) using
high-level encryption standards.
- Continuous Monitoring: Compliance isn't a one-time
event. You need automated tools to scan for misconfigurations or
unauthorized access in real-time.