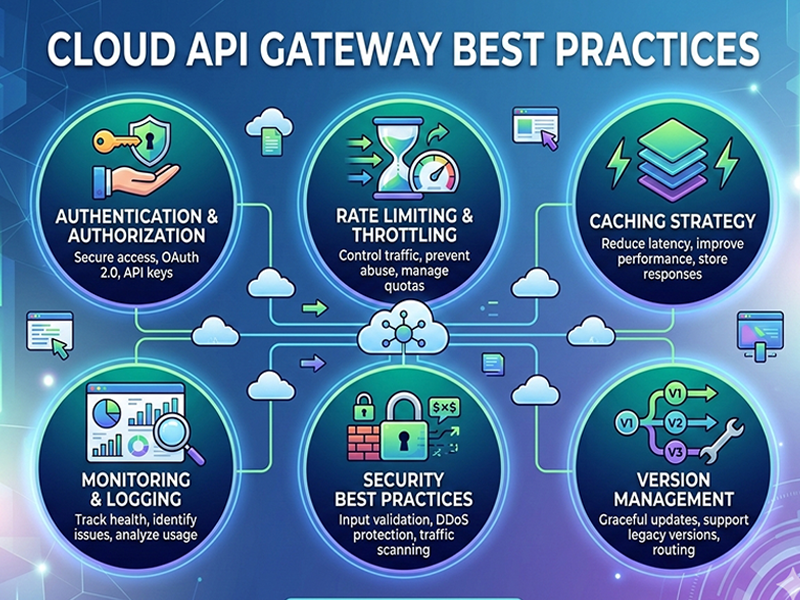
Cloud API Gateway Best Practices
The Cloud
API Gateway has evolved from a simple "traffic cop" into an
intelligent control plane. While traditional basics like authentication still
apply, modern best practices now focus on Zero Trust, AI-native
traffic, and Decentralized Governance.
1.
Security: Moving to Zero Trust
The gateway
is no longer just a wall; it’s a continuous verification engine.
- Centralize Auth, Decentralize
Enforcement:
Use a centralized identity provider (like Okta or Auth0) but enforce
validation at the gateway using short-lived JWTs (JSON Web Tokens).
- Apply "Broken Object Level
Authorization" (BOLA) Checks: A top OWASP risk. Ensure the gateway doesn't just check
if a user is "logged in," but verifies they have the right to
access the specific resource ID in the request.
- Mutual TLS (mTLS): For internal
"East-West" traffic, enforce mTLS to ensure services only talk
to verified partners.
2.
Performance: Intelligent Edge Routing
Latency is
the silent killer of user experience.
- Global Edge Deployment: Deploy gateways in multiple
regions closer to your users to reduce the "speed of light"
delay.
- Semantic Caching: In 2026, gateways use AI to
understand the intent of a query. If two different prompts for an
LLM result in the same meaning, the gateway can serve a cached response,
saving massive compute costs.
- Connection Pooling: Maintain a "warm"
pool of connections to backend services to avoid the overhead of the
TCP/TLS handshake for every request.
3.
Traffic Management & Resilience
Don't let
one bad client take down your entire ecosystem.
- Adaptive Rate Limiting: Move beyond static "100
requests per minute." Use dynamic throttling that tightens during
high system load and relaxes when resources are plentiful.
- Circuit Breaking: If a backend service fails, the
gateway should "trip the circuit" and return a cached or
graceful error immediately, rather than letting requests pile up and cause
a cascading failure.