API Rate Limiting
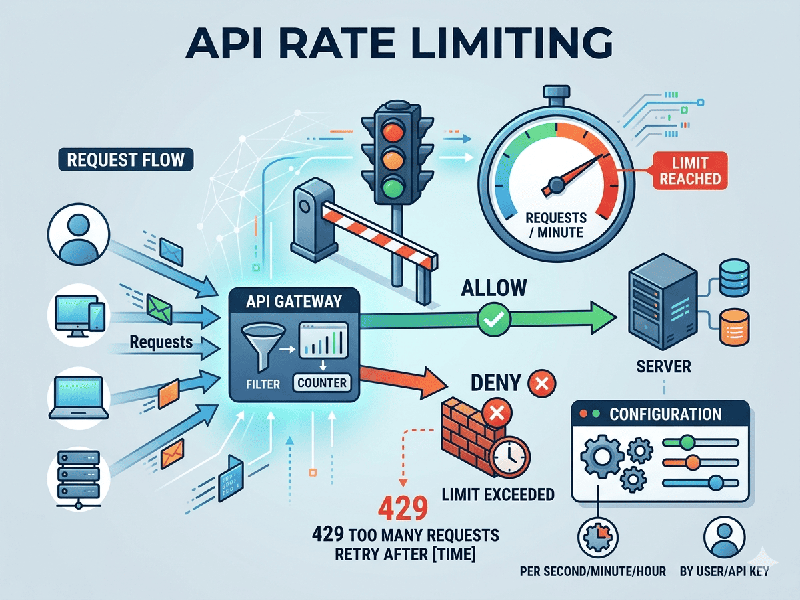
API rate
limiting has evolved from simple traffic control to a sophisticated security
and resource management layer. It is the process of controlling the number of
requests a client can make to a server within a specific timeframe to prevent
abuse and ensure system stability.
Why Rate
Limiting is Critical
- Preventing DoS/DDoS Attacks: It stops malicious actors from
overwhelming your infrastructure with a flood of requests.
- Cost Management: For cloud-native architectures,
it prevents "runaway" scaling costs triggered by automated
scripts or inefficient integrations.
- Fair Usage: Ensures that a single
"noisy neighbor" doesn't consume all available resources,
maintaining a high Quality of Service (QoS) for all users.
- Monetization: Acts as the enforcement
mechanism for tiered API pricing (e.g., Free vs. Pro tiers).
Core Rate
Limiting Algorithms
The choice
of algorithm depends on how strictly you need to control the flow of traffic.
1. Token
Bucket
The system
maintains a "bucket" that holds tokens. Each request consumes one
token. Tokens are refilled at a fixed rate.
- Pros: Allows for occasional
"bursts" of traffic if tokens have accumulated.
- Cons: Requires careful tuning of
bucket size to prevent resource exhaustion during bursts.
2. Leaky
Bucket
Requests
enter a bucket and are processed at a constant, "leaking" rate. If
the bucket is full, new requests are discarded.
- Pros: Smooths out traffic spikes into
a consistent flow.
- Cons: Does not allow for any
bursting, which can frustrate users during high-activity periods.
3. Fixed
Window Counter
The timeline
is divided into fixed intervals (e.g., 60 seconds). Each window has a set
limit.
- Pros: Extremely simple to implement.
- Cons: Vulnerable to a "boundary
spike"—a user could double their limit by sending requests at the
very end of one window and the start of the next.
4.
Sliding Window Log / Counter
A more
precise method that tracks the timestamp of each request or uses a weighted
average of the current and previous windows.
- Pros: Eliminates the boundary spike
issue and provides a smoother user experience.
- Cons: Higher memory overhead as it
needs to track more metadata per user.