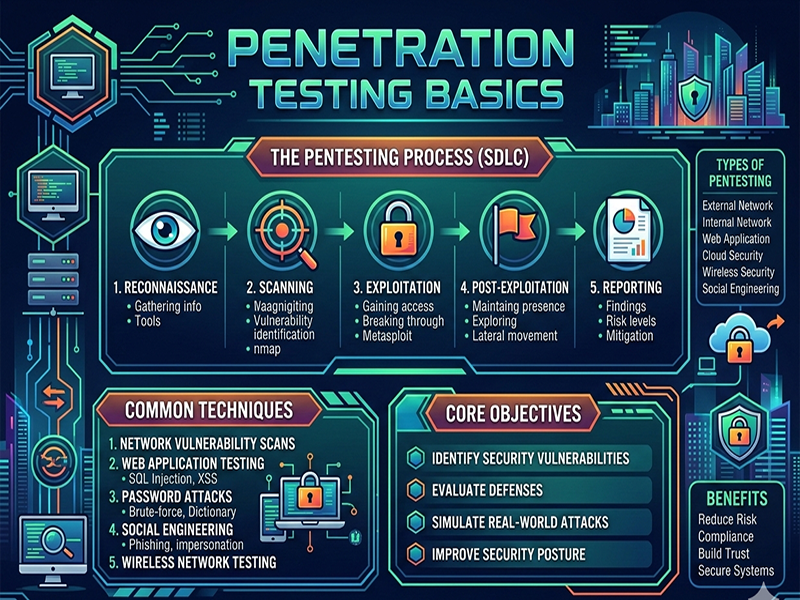
Penetration Testing Basics
Penetration
testing (or "pentesting") is essentially a controlled,
authorized attack on a computer system to find security weaknesses. Think of it
as hiring a professional locksmith to try and break into your house so they can
tell you exactly how they got in and how to fix the lock.
1. The
Five Phases of a Pentest
A
professional engagement usually follows a structured methodology to ensure
nothing is missed.
- Reconnaissance (Information
Gathering):
Collecting as much data as possible about the target. This includes IP
addresses, domain details, and employee info.
- Scanning: Using tools to identify open
ports and discover what services are running on the network.
- Gaining Access (Exploitation): This is where the
"hacking" happens. The tester uses vulnerabilities found in the
previous steps to bypass security controls.
- Maintaining Access: Seeing if it's possible to stay
in the system long-term (persistence) without being detected.
- Analysis & Reporting: The most important part.
Documenting how the hacks were done, what data was at risk, and how to
fix the holes.
2. Common
Areas of Testing
Pentesting
isn't just about "hacking a server." It covers various layers of an
organization:
- Web Applications: Checking for things like SQL
injection or Cross-Site Scripting (XSS).
- Network Services: Looking for weak passwords or
unpatched software in routers and switches.
- Social Engineering: Testing the "human
firewall" by sending phishing emails or trying to tailgating into a
secure building.
- Wireless: Cracking Wi-Fi encryption or
finding unauthorized "rogue" access points.
3. Why it
Matters
Compliance
is a big driver (like PCI-DSS or HIPAA), but the real value is proactive
defense. It’s much cheaper to pay a pentester to find a bug today than it
is to pay a ransom to a hacker tomorrow.
Important
Note: Always ensure
you have written permission (a "Rules of Engagement" document)
before testing any system you don't own. Without it, it's just illegal hacking.